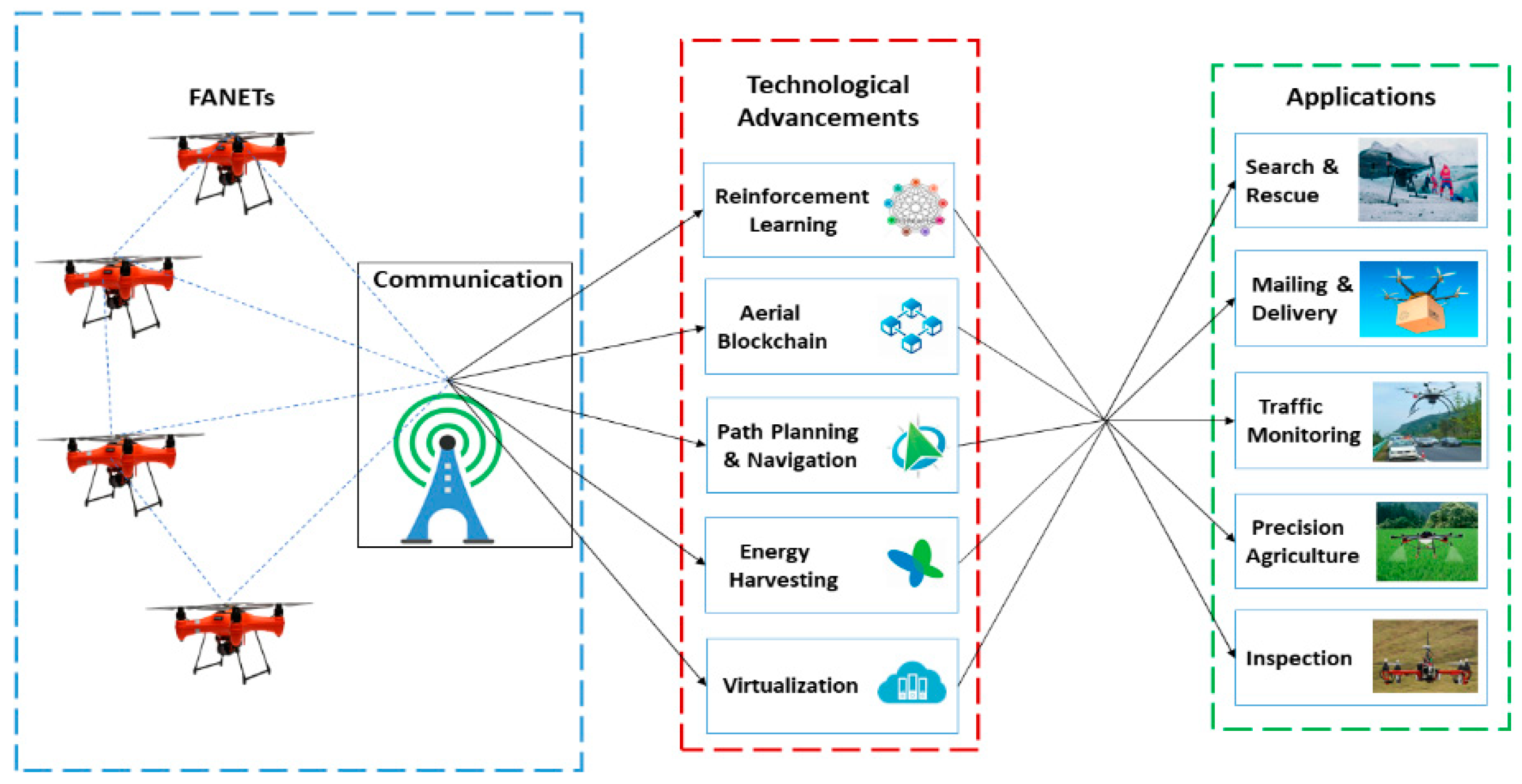
Drones | Free Full-Text | A Review on Communications Perspective of Flying Ad-Hoc Networks: Key Enabling Wireless Technologies, Applications, Challenges and Open Research Topics
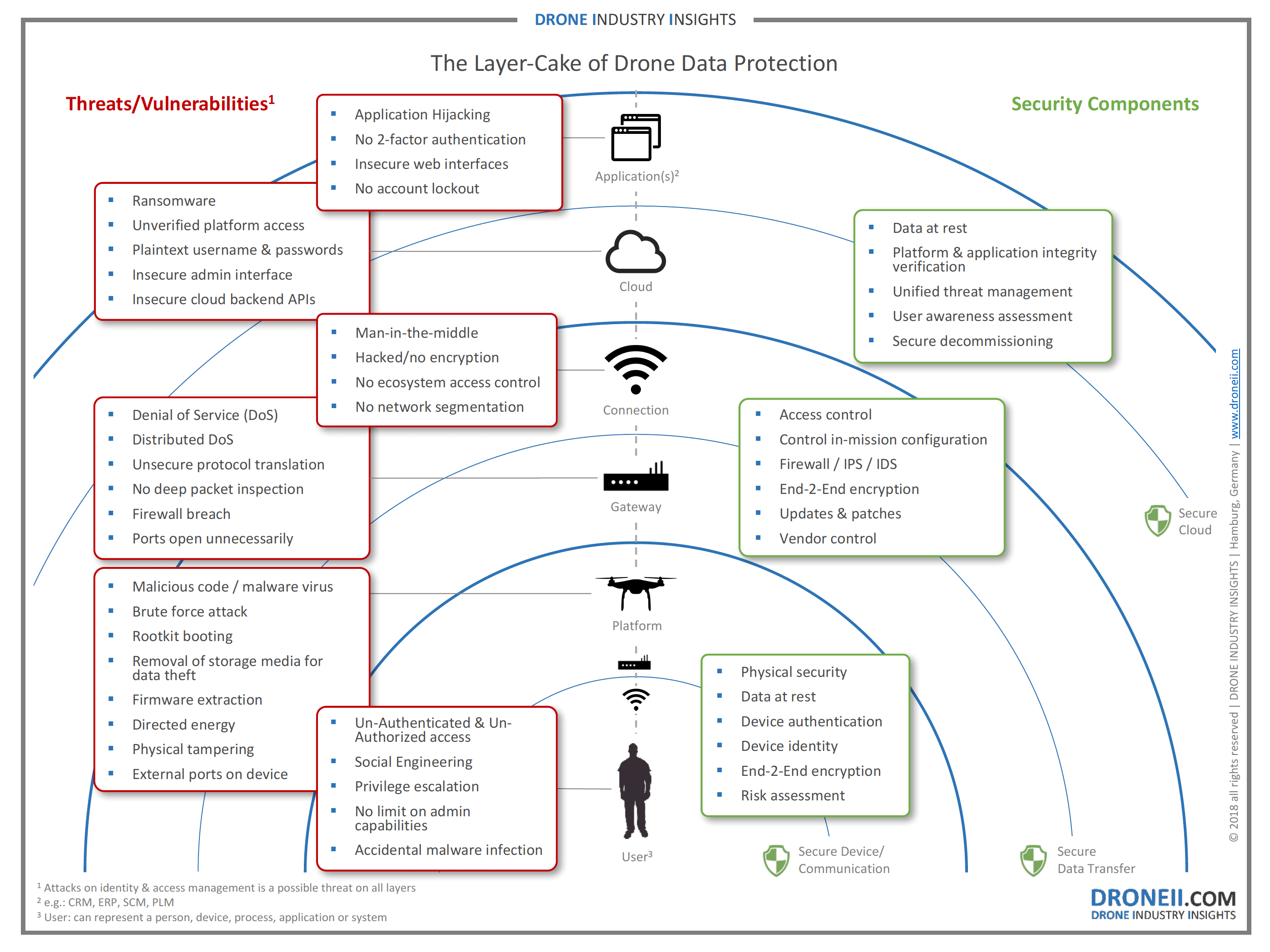
Drone Hacking and Cyber Warfare: Understanding the Potential Threats to National Security | by 0xSRF | Medium

Sensors | Free Full-Text | An Efficient Authenticated Key Agreement Scheme Supporting Privacy-Preservation for Internet of Drones Communications

Tech Times | Companies try hijacking and shooting drones - To keep flying objects out of high-risk areas | News | Jamaica Gleaner